For the last 6 months, my colleagues at Arco IT and I have been helping one of our clients develop their security monitoring capabilities using Azure Sentinel, a Microsoft cloud-based SIEM. For any clarification on what Sentinel is refer to the previous articles that present the Microsoft SIEM platform. In this article, I will explain how easily Azure Sentinel can be used to investigate security alerts.
Security Alerts in Sentinel
Azure Sentinel provides a simple user friendly service for handling incidents and investigating security events. After the initial setup of Sentinel (i.e. create Log Analytics Workspace, connect the log sources, create analytics rules to detect the targeted activities ), you can use the Sentinel “Investigations” pane to begin your investigations.
Assuming an analytics rule has “fired”, you will see incidents populating this pane. They will be named according to the analytics rule name and will have an Incident ID, as seen in Figure 1.
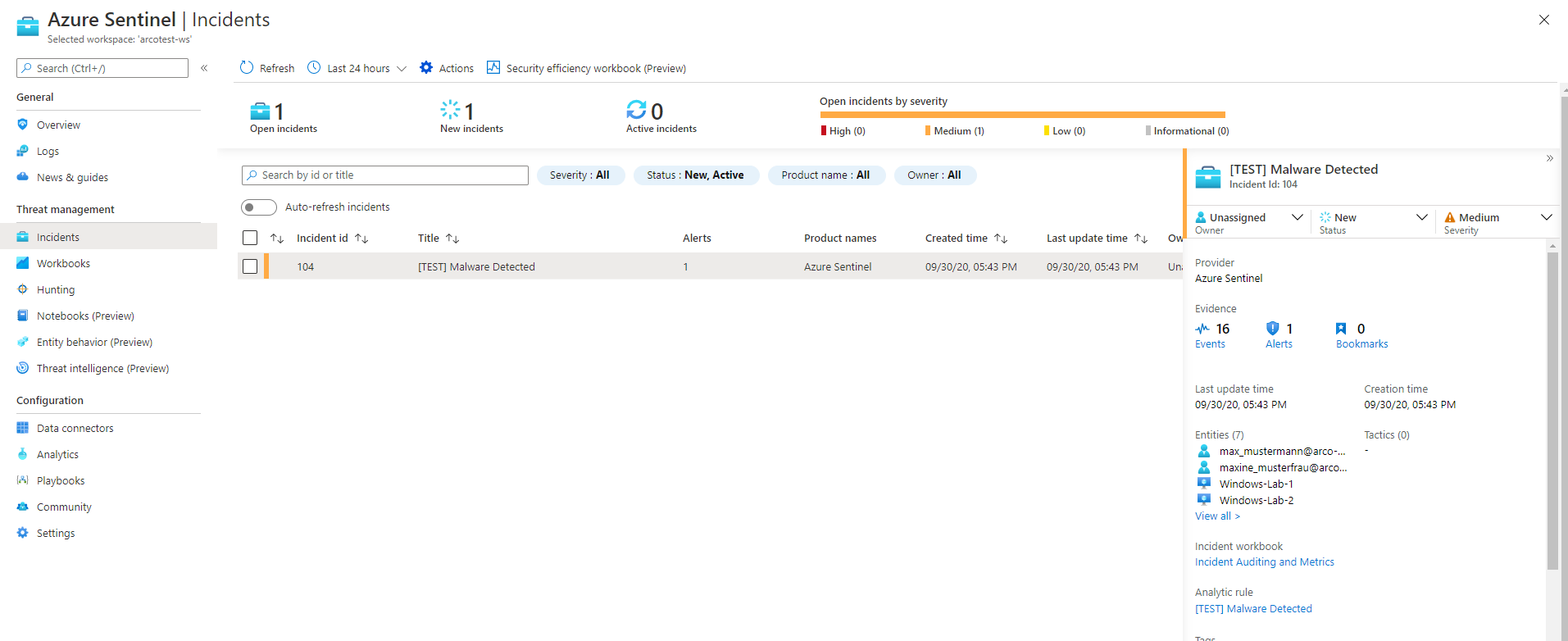
Figure 1
As you can see, the Incident pane provides a lot of information. In the middle are all the incidents that match the current filter settings. On the right, the details pane provides information about the specific incident selected in the list. It shows e.g. Owner, Status and Severity. These three values can be changed on the top part of the incident details pane. Owner is the account responsible for this incident. Status is the state of the incident which progresses from New to Open to Closed. Severity is the incident’s severity determined by default through the analytics rule with a selection of Low, Medium, High and Informational (in the case if example incident 104, it is Medium).
Additionally, you can see the number of alerts that are linked to this incident, the number of events (activities or logs) that are associated with this incident, the Entities assigned, and the tactics associated. These are based on the industry standard Mitre Att&ck framework. For more information see attack.mitre.org.
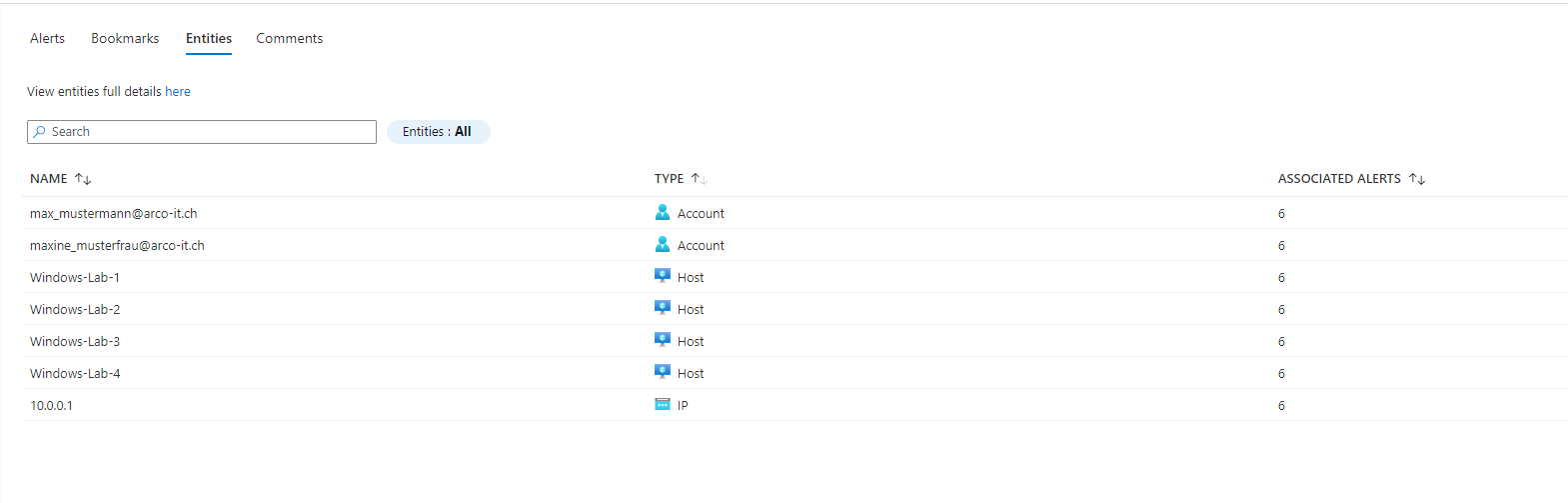
Figure 2
Entities are the objects that are related to these incidents. For example, the system identifies IP addresses, user accounts, host names. These can be used to cross-reference between incidents. The incident we can see in Figure 2 has Account, Host and IP entities. In a future installment of this series, we will talk about the Entity Behavior analysis features.
Incident Deep Diving
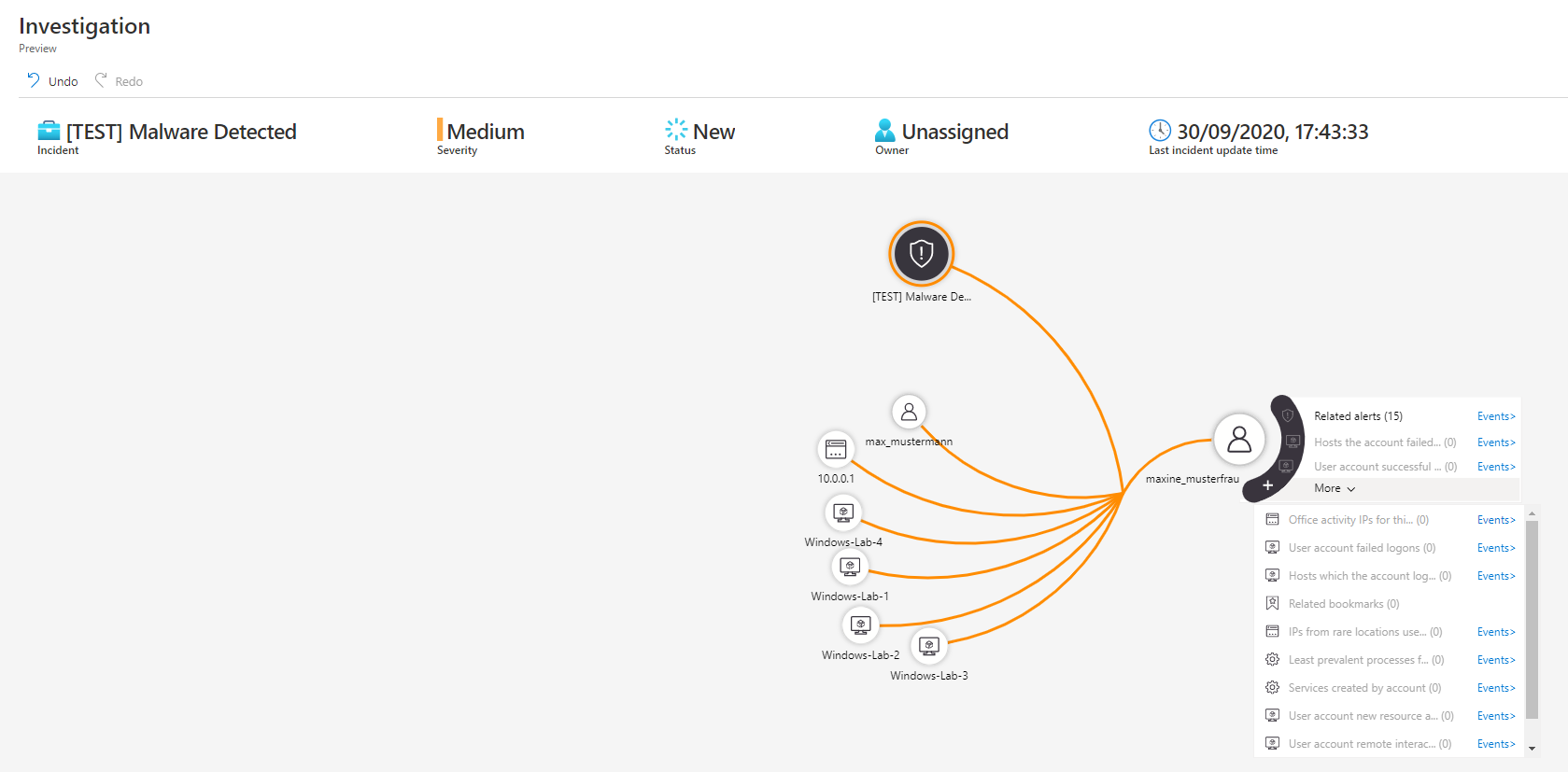
Figure 3
The Investigation pane (see figure 3) can be accessed by clicking the blue “Investigate” button on the Incidents page. This pane can be used to find connections between incidents and entities using a visual layout that can be customized with other information sources.
When an entity is clicked, additional data will be shown and deep dives for that entity can be launched. In our Figure 3 example you can see the entity maxine_musterfrau being investigated and a list of predefined queries can be run for things like Office Activity, Failed Logons, etc. relating to this user’s account.
Additionally, if required information cannot be found from within the Investigation pane, any log analytics queries can be run using the entities to perform more flexible searches. Using our example, an analyst could search for logs from the lab machines that were named in the incident to determine if they are behaving suspiciously. For detailed documentation on the Kusto Query Language used by Log Analytics, please refer to the Microsoft Documentation here.
What Next? Stay Tuned
In a future installment of this series, we will write about the Entity Behavior analysis features of Microsoft’s Azure Sentinel. Arco IT is a leader in the DACH region cloud-based security monitoring, and we are always there for your IT Security Service needs. Contact us for a free consultation.