Cyber incidents are the most common risk for companies and SMEs in Switzerland, with mostly far-reaching consequences. These range from business interruptions to ransom demands. However, a large part of cyber attacks can be avoided with just two simple measures.
Cyber attacks are usually carried out via a phishing email. The attackers lure the user to fake websites, for example. If the user then logs in there, the attackers can steal the password and use it to penetrate the company’s systems. The systems and data are then encrypted in such a way that the user or even the entire company can no longer work. After that, the attackers blackmail the company and demand a ransom payment. Only after the payment is received do they provide the codes, which the company can then use to restore its data and get the systems up and running again. Recently, the data is also sold or published to build up additional pressure and enable further revenue for the attackers.
Two protective pillars

The consequences of cyber-attacks are business-threatening for SMEs. Apart from ransom payments above 100,000 Swiss francs even for smaller companies, there are also problems with business interruptions, delayed production, competitive disadvantages, and possibly even legal consequences.
Although there are simple and effective means of protection, their use is only found in a few SMEs. With the following two pillars, two thirds of all cyber-attacks can be avoided.
First pillar: Additional protection for access
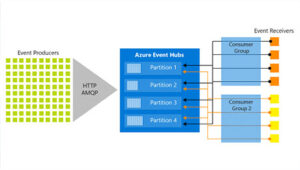
Attacks through stolen passwords can be prevented with multifactor authentication (MFA). MFA effectively protects access by means requiring an secondary feature on top of the usual password. This is something we are often already familiar with from online banking, for example when an SMS verification number is used. How well this protection works is visible when you look at evaluations by Microsoft’s security teams. Security groups have calculated that users without MFA are on average one thousand times more likely to be victims of hacking compared to users with MFA. A more secure yet convenient option is to use an authentication app. This can, for example, allow access by tapping on the cell phone or, in some cases, even on the smartwatch. MFA is available free of charge in many systems and users get used them easily.
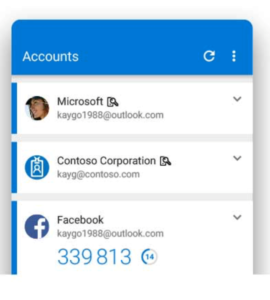
MFAs come in a variety of designs, not all of which provide the same level of security.
One-time code: One-time codes are sent via SMS and then manually typed into the computer. Unfortunately, mobile standards do not provide good protection for SMS data, so such solutions are not recommended.
Authentication app with one-time codes: These apps are loaded onto the cell phone and connected to the corresponding service (for example, accounting software) using a QR code. Subsequently, a new one-time password is generated every 30 seconds. The codes are generated based on a key that is known only to the user and server. The user types in the current code after entering the password.
Authentication app with confirmation click: After logging in to the relevant service, the registration is approved or rejected via the cell phone. If you have a smartwatch, you may be able to approve it directly on your wrist without having to look for your cell phone.
Physical Key: This type of MFA enables secure access directly on the hardware. The physical login is protected by a special USB stick or smartcard . This variant is also secure because the data exchange takes place directly via the hardware.
Device Management Software: Device management software offers the most comfortable way to protect corporate data, since the device (PC, laptop, smartphone, tablet) itself is the second factor. For this purpose, a digital certificate is installed on the device. When users log in with such a device, they only need the password and still have the security of MFA.
It should be noted that each additional logon step increases security and makes it more difficult to access data. In addition, MFA is a good and cost-effective way for companies to securely protect sensitive data and personal information.
Second pillar: Protecting employees
Regarding the protection of employees, the goal is to prevent phishing emails from reaching the users. Anti-phishing filters in e-mail systems provide initial protection. If emails do get through the firewalls and mail filters, users should be alert and respond correctly.
The mail filters can prevent around 80 percent of all attacks. They do this by blocking e-mails that contain known phishing content. The e-mails are continuously compared with data on known attacks and, if necessary, sent to the trash or an electronic quarantine.
The second stage, however, remains the user, as he or she is expected to react correctly in the event if a malicious email does come through anyway. To do this, he must be able to recognize dangerous content and report the e-mail to the responsible IT department or destroy it.
Phishing tests are suitable for an initial check of the security awareness of all employees. A one-time phishing test shows what the current level of employees is in terms of recognizing phishing and malware. Typically, it shows a “phishing rate” of 35 to 40 percent, which means that more than a third of all employees do not recognize the attacks and allow themselves to be directed to the fake websites. There, they often enter their passwords without a second thought.
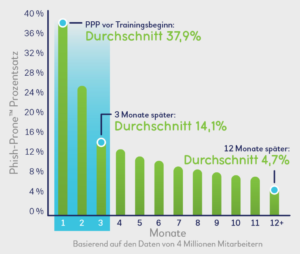
Security awareness training can be used to train employees specifically in this area over a period of time. Regular and targeted phishing attacks are carried out via an online platform. If the employee does not recognize the e-mail as malicious, he learns what he should have paid attention to thanks to visual highlighting of clues in the e-mail. Additional training sessions with different focal points (phishing, ransomware, etc.) improve the awareness of individual employees. These regular training sessions show make the phishing rate drop to less than five percent after one year.
The entire learning process should be designed as a cycle and take place on a regular basis. E-learnings, videos, games, posters, or newsletters are used to sensitize users to specific content. Subsequently, new, and more difficult phishing campaigns are carried out to test the employees again. The analysis of the campaigns shows exactly where weaknesses still exist, and which employees misjudge the emails. From these results, individual training campaigns are created, and all employees are tested again. The goal always remains to ensure that users recognize genuine phishing emails and react correctly.

There are various providers for such security training, and the costs for online tests and training are only a few francs per user and month. Compared to the above-mentioned costs of a successful hacker attack, this small investment is very worthwhile.
Arco IT provides support for both topics. We can help with protecting your accesses and we can run awareness training campaigns for you. Contact us for further information at: info@arco-it.ch
This article is adapted from ‘KMU Magazin Nr. 04/05, April/Mai 2021’